Cyber Intelligence Report
: Analysis on the Market, Trends, and TechnologiesThe cyber intelligence market shows rapid commercialization and concentration, with a 2024 market size of $11,580,000,000 and divergent forecasts pointing to multi-billion expansion driven by AI analytics and external risk management; one projection places the segment at $31,360,000,000 by 2029. Market analysis and patent activity indicate a shift from signature-based collection to predictive, workflow-centric intelligence supported by growing AI investment (internal filings show 419 granted patents and a 14.5% year-over-year increase in AI cyber defense funding since 2023).
We updated this report 37 days ago. Noticed something’s off? Let’s make it right together — reach out!
Topic Dominance Index of Cyber Intelligence
The Topic Dominance Index trendline combines the share of voice distributions of Cyber Intelligence from 3 data sources: published articles, founded companies, and global search
Key Activities and Applications
- Real-time threat hunting and IoC enrichment — Automated ingestion and enrichment of indicators from clear, deep and dark web sources shortens dwell time and feeds SOC triage pipelines, a capability commercialized by specialized collectors and indexing platforms Cybersixgill, a Bitsight Company.
- External attack surface management (EASM) and digital risk protection (DRP) — Continuous discovery of exposed assets, certificates, DNS artifacts, and impersonation campaigns now underpins underwriting and breach-avoidance programs Cyberint, a Check Point Company.
- Threat-informed defense (TID) and detection engineering operationalization — Mapping adversary procedures to deployed controls (technique-to-coverage calculations) turns intelligence into measurable risk reduction for SOCs and red teams Tidal Cyber.
- Predictive vulnerability prioritization and dynamic risk scoring — Intelligence signals are used to escalate the few percent of vulnerabilities that present real exploitation risk, improving remediation ROI and compliance outcomes
- Skill validation, cyber ranges, and crisis simulation — Live-fire exercises and incident simulations create measurable operational readiness and close the workforce gap highlighted in policy analysis Cyber Workforce Strategies Should Produce at Scale.
Emergent Trends and Core Insights
- AI-first analyst augmentation — Firms report that 90% of enterprises are piloting or implementing AI across intelligence workflows, shifting human roles toward decisioning and exception handling while machines perform scale tasks.
- Fusion of CTI, TIP, EASM and DRP into unified platforms — Buyers prefer platforms that convert multiple signals into prioritized actions and playbooks, reducing vendor sprawl and manual correlation efforts.
- On-premises persistence with cloud acceleration — Regulated industries maintain significant on-premises deployments for data sovereignty, even as cloud-native analytics grow faster; forecasts show on-premises retaining a majority share while cloud solutions post higher CAGR in many forecasts Cyber Threat Intelligence Market Size, Growth Analysis 2035.
- OT/ICS and identity risk intelligence specialization — Targeted intelligence for industrial protocols and identity compromise are rising as priority verticals because the impact of attacks is operational and immediate ICS-Security.
- Intelligence-led insurance underwriting and continuous monitoring — Underwriters increasingly require dynamic telemetry and quantified risk models for pricing, leading to integrated insurance-security offerings and parametric products.
Technologies and Methodologies
- Graph analytics and knowledge-graph correlation engines — Relationship mapping across IOCs, infrastructure, malware families and personas enables attack-path prediction and enriched context for automated playbooks
- Proprietary AI models and XAI for triage and justification — Explainable ML models are being embedded to produce prioritized findings and to provide analysts and executive stakeholders with evidence chains for action
- Federated learning and data-sovereign inference — Approaches that train models without centralizing raw telemetry aim to satisfy regulatory constraints while benefiting from cross-organization learning.
- Deception and adversary simulation — Adaptive honeypots and interactive decoys collect attacker behavior to refine TTP libraries and to validate detection hypotheses
- Automated attack surface discovery and telemetry fusion — Continuous scanning of certificates, DNS, cloud misconfigurations and third-party exposures feeds scoring engines that drive both SOC and insurance workflows.
Cyber Intelligence Funding
A total of 230 Cyber Intelligence companies have received funding.
Overall, Cyber Intelligence companies have raised $14.2B.
Companies within the Cyber Intelligence domain have secured capital from 761 funding rounds.
The chart shows the funding trendline of Cyber Intelligence companies over the last 5 years
Cyber Intelligence Companies
- Cyber Intel Matrix - CIM
Cyber Intel Matrix offers a focused CTI platform that targets ICS and IoT attack surfaces, sending prioritized indicators directly to SIEM and SOAR stacks to reduce false positives and improve SOC signal-to-noise. The company emphasizes subscriber-specific relevance by ingesting client infrastructure metadata at onboarding, which narrows alerts to only those assets that matter operationally. This tight mapping to customer topology makes its intelligence immediately actionable for critical-infrastructure operators - Cytidel
Cytidel markets vulnerability threat intelligence that ranks the small subset of vulnerabilities that pose real exploitation risk, claiming earlier detection of emergent exploit activity and improved prioritization for patch programs. The product is built to feed remediation ticketing and measurement frameworks so security teams can demonstrate quantifiable risk reduction to executives and auditors. Cytidel's positioning addresses the remediation overload problem by converting intelligence into deterministic action queues - Intelici
Intelici deploys an AI engine within carrier networks to detect early propagation patterns of threats without payload inspection, delivering content-agnostic early warnings for encrypted traffic flows and lateral movement. That traffic-propagation approach provides a distinct detection vector for telecommunication operators and large service providers who must monitor at scale while preserving privacy. The patent-backed technique helps fill a monitoring gap where payload visibility is constrained - Cogility Software
Cogility combines no-code modeling and behavioral analytics in a continuous decision intelligence platform used for insider risk and third-party risk assessment, enabling organizations to operationalize signals into case-driven workflows. The platform's strengths lie in rapid model authoring and full audit trails that support governance and compliance reporting. Cogility's approach suits government and enterprise environments that require traceable adjudication of risk findings
Gain a better understanding of 2.8K companies that drive Cyber Intelligence, how mature and well-funded these companies are.
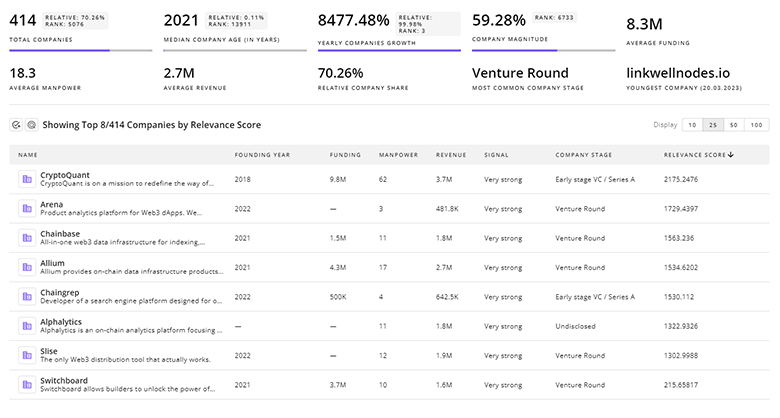
2.8K Cyber Intelligence Companies
Discover Cyber Intelligence Companies, their Funding, Manpower, Revenues, Stages, and much more
Cyber Intelligence Investors
Gain insights into 793 Cyber Intelligence investors and investment deals. TrendFeedr’s investors tool presents an overview of investment trends and activities, helping create better investment strategies and partnerships.
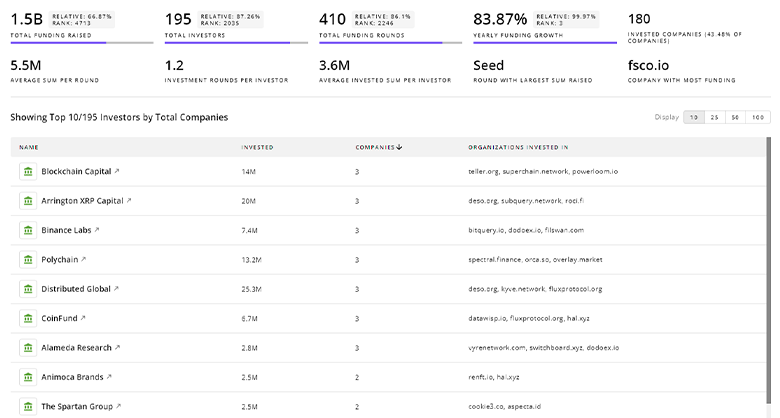
793 Cyber Intelligence Investors
Discover Cyber Intelligence Investors, Funding Rounds, Invested Amounts, and Funding Growth
Cyber Intelligence News
Gain a competitive advantage with access to 2.9K Cyber Intelligence articles with TrendFeedr's News feature. The tool offers an extensive database of articles covering recent trends and past events in Cyber Intelligence. This enables innovators and market leaders to make well-informed fact-based decisions.
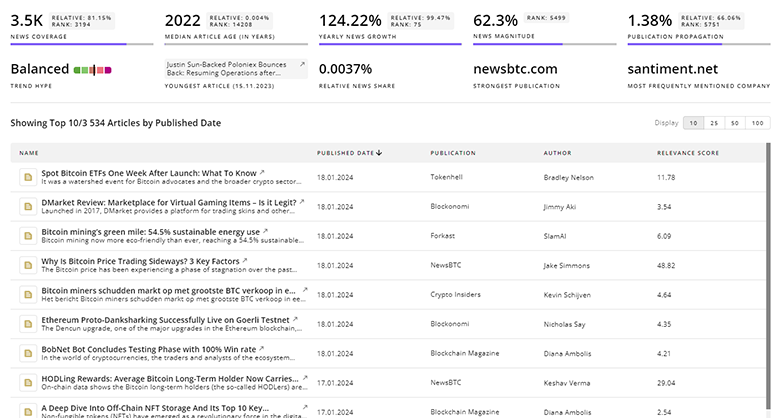
2.9K Cyber Intelligence News Articles
Discover Latest Cyber Intelligence Articles, News Magnitude, Publication Propagation, Yearly Growth, and Strongest Publications
Executive Summary
Investment and innovation in cyber intelligence concentrate where intelligence becomes measurable action: reducing time-to-remediation, quantifying exposure against adversary procedures, and integrating signals into policy and insurance workflows. Organizations that align budgeting and procurement to acquire fused intelligence platforms while selectively partnering with niche data providers (OT/ICS, identity compromise, early propagation detection) will gain a defensible operational advantage. Boards and CISOs should reframe cyber intelligence purchases as investments in decision velocity and measurable risk reduction, allocate budget to experiment with model explainability and data-sovereign deployments, and prioritize rigorous readiness programs that connect intelligence outputs to both technical playbooks and executive reporting.
We seek partnerships with industry experts to deliver actionable insights into trends and tech. Interested? Let us know!