Social Engineering Report
: Analysis on the Market, Trends, and TechnologiesThe domain of social engineering within cybersecurity is experiencing significant growth and evolution. With 1135 companies active in this sector, social engineering has become a critical aspect of digital security, exploiting human psychology to bypass technical safeguards. This comprehensive analysis reveals that social engineering is intricately linked to broader cybersecurity themes, including military & defense and risk management. Key trends such as phishing, spear phishing, and ethical hacking demonstrate the sector’s complex interconnectivity. Market indicators suggest a surge in interest and activity, positioning social engineering as a vital topic in today’s business environment. Growth in funding, new company establishments, and media coverage highlight its escalating importance. As social engineering threats become more sophisticated, businesses are urged to enhance their vigilance and proactive measures to protect their operations and data integrity.
456 days ago, we last updated this report. Notice something that’s not right? Let’s fix it together.
Topic Dominance Index of Social Engineering
To gauge the influence of Social Engineering within the technological landscape, the Dominance Index analyzes trends from published articles, newly established companies, and global search activity
Key Activities and Applications
- Phishing and Spear Phishing: Extensive efforts in combating deceptive practices aimed at obtaining sensitive information.
- Ethical Hacking: Employing controlled hacking techniques to identify and address security vulnerabilities.
- Risk Management: Developing strategies to manage potential threats associated with human factors in cybersecurity.
- Cybersecurity Training: Offering comprehensive educational programs to improve security awareness and skills.
- Military & Defense Applications: Implementing social engineering tactics for national security and intelligence purposes.
- Insurance and Financial Protections: Crafting insurance products and services to mitigate losses from social engineering attacks.
Emergent Trends and Core Insights
- Growing Intersectoral Integration: A noticeable blend of social engineering practices across various cybersecurity domains.
- Increased Funding and Investor Confidence: Reflecting the sector's potential for expansion and innovation.
- Media Presence and Public Awareness: Enhanced understanding and coverage of social engineering threats.
- Human Factor Emphasis: Recognizing the critical role of human psychology in cybersecurity defenses.
- Evolution of Attack Techniques: Adaptation and sophistication of social engineering methods to outpace conventional security measures.
Technologies and Methodologies
- Advanced Phishing Detection: Utilization of AI and machine learning to identify and prevent phishing attempts.
- Simulation and Training Platforms: Interactive tools to simulate attacks and train personnel in threat recognition.
- Vulnerability Assessments: Comprehensive evaluations to identify weaknesses that could be exploited through social engineering.
- Incident Response and Forensics: Specialized approaches to address and investigate security breaches involving human manipulation.
- Multi-Factor Authentication (MFA): Enhancing security protocols to counteract social engineering by verifying user identities through multiple methods.
Social Engineering Funding
A total of 80 Social Engineering companies have received funding.
Overall, Social Engineering companies have raised $2.6B.
Companies within the Social Engineering domain have secured capital from 230 funding rounds.
The chart shows the funding trendline of Social Engineering companies over the last 5 years
Social Engineering Companies
Get detailed analytics and profiles on 1.1K companies driving change in Social Engineering, enabling you to make informed strategic decisions.
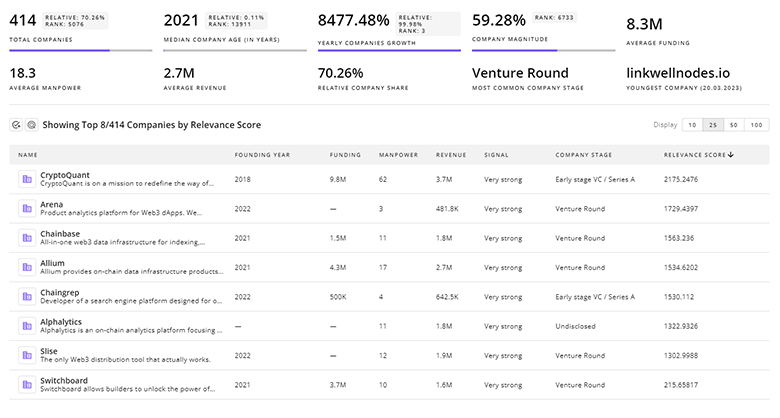
1.1K Social Engineering Companies
Discover Social Engineering Companies, their Funding, Manpower, Revenues, Stages, and much more
Social Engineering Investors
TrendFeedr’s Investors tool provides an extensive overview of 111 Social Engineering investors and their activities. By analyzing funding rounds and market trends, this tool equips you with the knowledge to make strategic investment decisions in the Social Engineering sector.
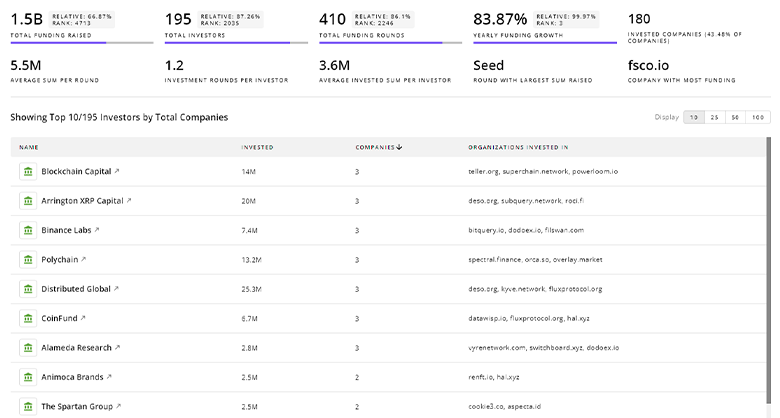
111 Social Engineering Investors
Discover Social Engineering Investors, Funding Rounds, Invested Amounts, and Funding Growth
Social Engineering News
Explore the evolution and current state of Social Engineering with TrendFeedr’s News feature. Access 13.8K Social Engineering articles that provide comprehensive insights into market trends and technological advancements.
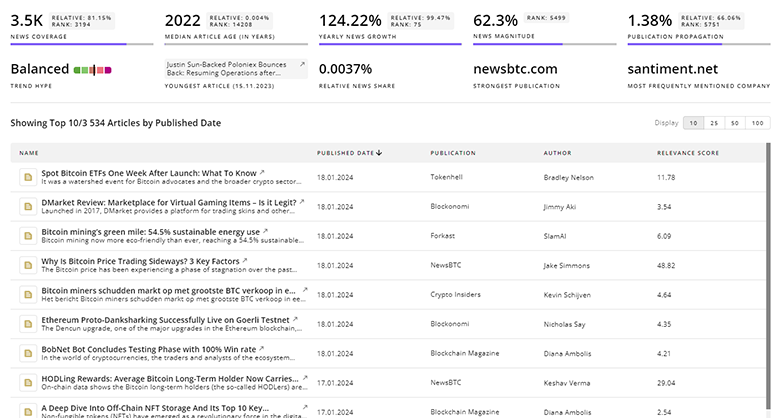
13.8K Social Engineering News Articles
Discover Latest Social Engineering Articles, News Magnitude, Publication Propagation, Yearly Growth, and Strongest Publications
Executive Summary
The importance of addressing social engineering within the cybersecurity landscape cannot be overstated. As companies continue to grapple with the human element of security, the need for advanced training, awareness, and technological solutions becomes paramount. The sector's growth trajectory, backed by significant investment and broadening scope, underscores the urgency for businesses to adopt a vigilant and proactive stance. By understanding the nuances of human psychology and its intersection with technology, organizations can fortify their defenses against the increasingly sophisticated tactics of social engineering.
We're looking to collaborate with knowledgeable insiders to enhance our analysis of trends and tech. Join us!