Phishing-resistant Authentication Report
: Analysis on the Market, Trends, and TechnologiesThe phishing-resistant authentication market is entering a phase of measurable commercialization: market analysis estimates a market size of $2,400,000,000 with a 13.4% CAGR, indicating sustained buyer willingness to replace weak credentials with cryptographic and device-bound methods. Industry forecasts focusing on AI-enabled solutions project rapid scale from $2.17B in 2024 to $10.59B by 2033 (approx. 18.3% CAGR), which, together with observed adoption signals (Okta FastPass adoption rising to 13.3% and phishing-resistant methods covering 14% of deployments), places organizations that integrate cryptographic passkeys, device attestations, and behavioral telemetry on a path to materially reduce account takeover exposure.
The last time we updated this report was 103 days ago. If there’s something missing or off, your tips are welcome!
Topic Dominance Index of Phishing-resistant Authentication
The Dominance Index for Phishing-resistant Authentication merges timelines of published articles, newly founded companies, and global search data to provide a comprehensive perspective into the topic.
Key Activities and Applications
- FIDO2 / Passkey rollouts for workforce and consumer sign-in. Enterprises deploy domain-bound public-key credentials to eliminate password replay and credential stuffing at scale; federal and large commercial rollouts demonstrate feasibility for thousands of users.
- Device-bound transaction signing and out-of-band confirmation for high-value flows. Financial services replace SMS/OTP with cryptographic transaction confirmation or QR-based OOB that ties approval to the device and specific transaction details Phishing-Resistant Authentication Market Research Report 2033.
- Continuous, passive behavioral verification to detect session takeover. Background biometric and interaction telemetry (keystroke, mouse, touch patterns) enable step-up or silent re-authentication during anomalous sessions, reducing reliance on interruptive second factors.
- Identity and access convergence via ICAM and zero-trust orchestration. Organizations integrate passkeys, device posture checks, and adaptive policies at the authentication server layer to automate credential lifecycle and enforcement without wholesale IAM migration.
- Threat intelligence driven policy tuning and takedown integration. Real-time phishing monitoring and takedown feeds inform adaptive access rules (e.g. escalate to cryptographic sign-in when active PhaaS campaigns target an industry).
Emergent Trends and Core Insights
- AI accelerates both attack scale and defensive differentiation. Generative attack tooling fuels more convincing social engineering at scale, while defenders embed AI into biometric matching and behavioral risk scoring to reduce false positives and identify AiTM relays in real time Phishing-Resistant Authentication AI Market Research Report 2033.
- Regulatory and procurement mandates are shifting vendor selection toward cryptographic credentials. Government directives and payment-sector rules accelerate replacement of SMS/TOTP with FIDO-based passkeys and high-assurance MFA for critical users Phishing-Resistant authentication is taking off.
- A bifurcated market is forming: infrastructure providers vs. telemetry specialists. One segment commoditizes FIDO/Passkey plumbing; the other builds continuous assurance moats from behavioral datasets and low-latency models, creating acquisition targets and partnership windows (infrastructure needs telemetry to raise assurance). Market synthesis shows platform consolidation pressures driven by funding and enterprise procurement trends Token.
- Endpoint/edge protection (on-device verification) reduces reliance on gateway filtering. On-device URL/context checks and local cryptographic attestations block phishing attempts at the point of click rather than after inbox delivery.
- Adoption remains uneven; enterprise pilots are concentrated in high-risk verticals. BFSI, government, and healthcare lead deployments, while many SMEs delay due to integration costs and skill gaps—creating channel opportunities for no-code FIDO integration and managed services.
Technologies and Methodologies
- FIDO2 / WebAuthn (public-key cryptography bound to domain). Domain-bound private keys and attestations make credentials useless to attackers operating on spoofed sites and are now the baseline cryptographic method for phishing resistance Phishing-Resistant Multi-Factor Authentication (MFA) Success Story.
- Device attestation and hardware-backed secure elements. Secure enclaves, TPMs, and certified security keys anchor private keys to devices and prevent remote export or cloning, a requirement for high-assurance transaction signing.
- Continuous behavioral authentication and passive biometrics. AI models ingest keystroke dynamics, mouse/touch patterns and background signals to create ongoing confidence scores that trigger adaptive controls or silent re-auth.
- On-device computer vision and link analysis at the point-of-click. Endpoint engines inspect rendered pages and UI elements to stop phishing before credential entry, reducing dependency on mail gateways alone PIXM.
- Risk-based adaptive authentication and zero-trust policy engines. Real-time signals (network context, device posture, behavioral score, threat intel) feed decision engines that raise or lower friction dynamically to protect sensitive assets.
Phishing-resistant Authentication Funding
A total of 180 Phishing-resistant Authentication companies have received funding.
Overall, Phishing-resistant Authentication companies have raised $34.2B.
Companies within the Phishing-resistant Authentication domain have secured capital from 869 funding rounds.
The chart shows the funding trendline of Phishing-resistant Authentication companies over the last 5 years
Phishing-resistant Authentication Companies
- Relock — Relock provides an API-level platform that claims rapid deployment of phishing- and session-hijacking resistance by controlling API permissions and embedding ephemeral, per-call encryption keys; the offering targets developer-facing APIs and customer portals where session hijack occurs post-login. Relock positions itself as a complementary layer to existing credentials, enabling protection for external partners and customers without large UX changes, which makes it attractive for service providers that cannot mandate hardware tokens and for buyers seeking a single-day deployment path.
- Secfense — Secfense focuses on enterprise passkey adoption by adding a security broker layer that overlays existing IAM (Active Directory, Okta, Entra) so organizations can deliver FIDO-based authentication to web, legacy and VPN applications without app rewrites. The company’s model reduces migration risk and preserves control of identity data while enabling passkey rollout across complex estates, a high-value proposition for regulated enterprises.
- Twosense — Twosense delivers continuous authentication using passive behavioral biometrics (typing, mouse) to validate the human presence throughout sessions; the product targets contact centers, healthcare and BPOs that require low friction and high assurance. The company emphasizes rapid software-only deployment and claims enterprise-grade scaling for environments that need continuous session protection rather than point-in-time checks.
- Infinipoint — Infinipoint offers a Zero Trust Access Platform that combines passkeys with device posture and one-click remediation to enforce phishing-resistant access and device hygiene. The platform integrates passkey authentication into a broader device-aware access decision, which reduces successful account takeovers even when initial credentials or sessions become exposed.
- Airome Technologies — Airome focuses on transaction confirmation across digital banking channels with a product that cryptographically binds transaction details to the approving device (reducing fraud by their reported ~75% metric). Its transaction-signing approach addresses the exact vector phishers exploit when they intercept or relay approval flows, making Airome relevant for banks and payment platforms migrating away from OTPs.
Delve into the corporate landscape of Phishing-resistant Authentication with TrendFeedr’s Companies tool
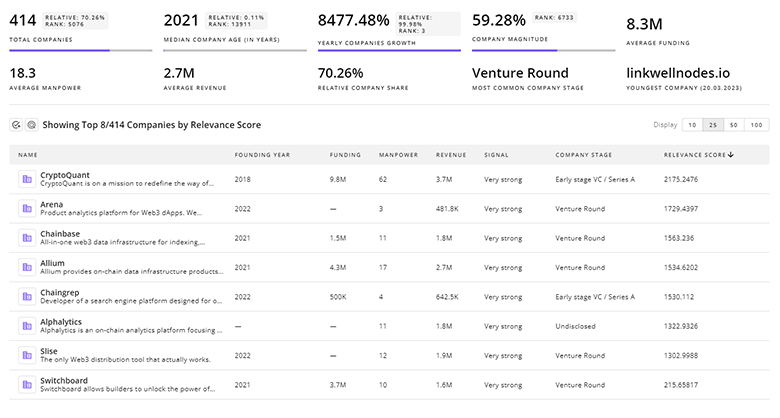
1.0K Phishing-resistant Authentication Companies
Discover Phishing-resistant Authentication Companies, their Funding, Manpower, Revenues, Stages, and much more
Phishing-resistant Authentication Investors
TrendFeedr’s Investors tool provides insights into 1.7K Phishing-resistant Authentication investors for you to keep ahead of the curve. This resource is critical for analyzing investment activities, funding trends, and market potential within the Phishing-resistant Authentication industry.
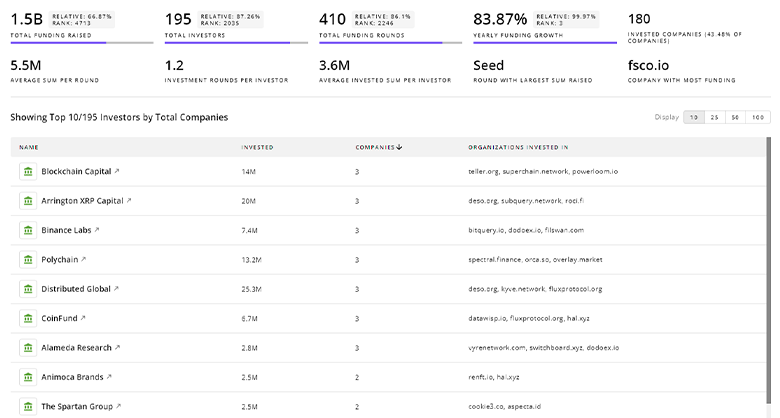
1.7K Phishing-resistant Authentication Investors
Discover Phishing-resistant Authentication Investors, Funding Rounds, Invested Amounts, and Funding Growth
Phishing-resistant Authentication News
TrendFeedr’s News feature offers you access to 4.7K articles on Phishing-resistant Authentication. Stay informed about the latest trends, technologies, and market shifts to enhance your strategic planning and decision-making.
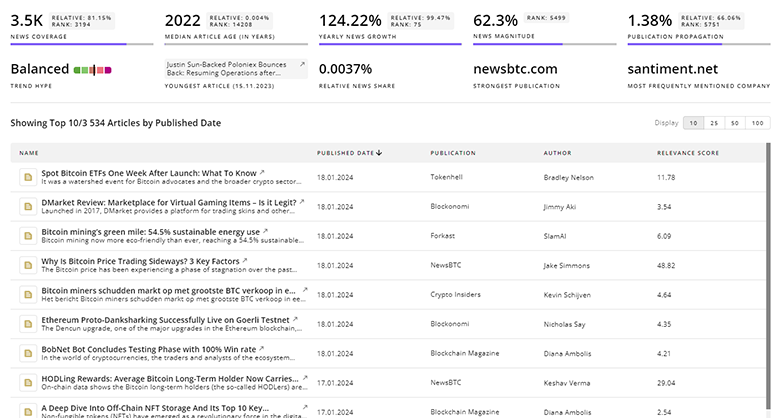
4.7K Phishing-resistant Authentication News Articles
Discover Latest Phishing-resistant Authentication Articles, News Magnitude, Publication Propagation, Yearly Growth, and Strongest Publications
Executive Summary
Phishing-resistant authentication now combines three practical levers: cryptographic credentials anchored to devices, continuous behavioral assurance, and endpoint-level context verification. Market dynamics and regulatory pressure favor rapid passkey adoption, yet real security gains come when organizations layer continuous telemetry and device posture checks on top of FIDO. Strategic priorities for business leaders are clear: accelerate passkey integrations where possible, fund behavioral telemetry pilots for high-risk user populations, and contract with partners that provide minimal-disruption deployment models or managed services to close skills and automation gaps. The firms that succeed will be those that make cryptographic, device-anchored authentication invisible to legitimate users while making attacks materially harder and more expensive for adversaries.
Are you an insider in the trends or tech industry? We’d love for you to contribute to our content.