Business Security Report
: Analysis on the Market, Trends, and TechnologiesThe business security sector is experiencing a significant surge in demand, reflecting the critical need for robust security measures in the face of escalating cyber threats and physical breaches. With over 2500 companies active in this space, the market is mature, yet it continues to grow and innovate, as evidenced by the 88.83% increase in global search interest over the past five years. The sector’s dynamism is fueled by substantial investments totaling $5.53 billion, indicating strong market confidence. The employment growth rate and extensive media coverage further underscore the industry’s vitality. This report synthesizes key activities, emergent trends, and prevalent technologies shaping the business security ecosystem, drawing insights from a wide array of companies engaged in safeguarding assets, data, and personnel.
This report was last updated 28 days ago. Spot an error or missing detail? Help us fix it by getting in touch!
Topic Dominance Index of Business Security
To identify the Dominance Index of Business Security in the Trend and Technology ecosystem, we look at 3 different time series: the timeline of published articles, founded companies, and global search. These timelines are normalized and combined to show a comprehensive view of the Business Security evolution relative to all known Trends and Technologies.
Key Activities and Applications
- Implementation of advanced cybersecurity solutions to combat the rise in cyber threats.
- Integration of surveillance and monitoring technologies for enhanced physical security.
- Development of access control systems for secure entry management.
- Deployment of alarm and intrusion detection systems for immediate threat response.
- Investment in fire and safety measures to protect infrastructure and personnel.
- Emphasis on business continuity planning and disaster recovery strategies.
- Provision of IT and network security audits to identify and mitigate vulnerabilities.
- Enhancement of data protection and privacy through encryption and secure data management.
Emergent Trends and Core Insights
- A shift towards AI and machine learning to predict and prevent security incidents.
- Adoption of cloud-based security solutions for scalable and flexible protection measures.
- Increased reliance on mobile and remote security management for on-the-go monitoring.
- Growth in the use of biometric security systems for reliable identity verification.
- Expansion of IoT security to cover a broader range of connected devices.
- Emphasis on comprehensive security training and awareness programs for employees.
- Collaboration between private and public sectors to standardize security protocols.
- Demand for integrated security systems that offer a unified view of threats and responses.
Technologies and Methodologies
- Utilization of blockchain technology for secure and transparent transactions.
- Deployment of smart security systems with automation and real-time alerts.
- Integration of cybersecurity and physical security for a holistic defense approach.
- Application of predictive analytics for proactive threat identification.
- Adoption of SASE (Secure Access Service Edge) platforms for network security.
- Implementation of zero-trust security models to minimize insider threats.
- Use of virtual and augmented reality for security training and simulation.
- Investment in quantum computing research to future-proof encryption methods.
Business Security Funding
A total of 114 Business Security companies have received funding.
Overall, Business Security companies have raised $5.6B.
Companies within the Business Security domain have secured capital from 256 funding rounds.
The chart shows the funding trendline of Business Security companies over the last 5 years
Business Security Companies
The Companies feature is a crucial part of TrendFeedr. It offers in-depth information about 2.6K companies working within Business Security and other trends and technologies. Identify and analyze innovators and key players in relevant industries more easily with this feature.
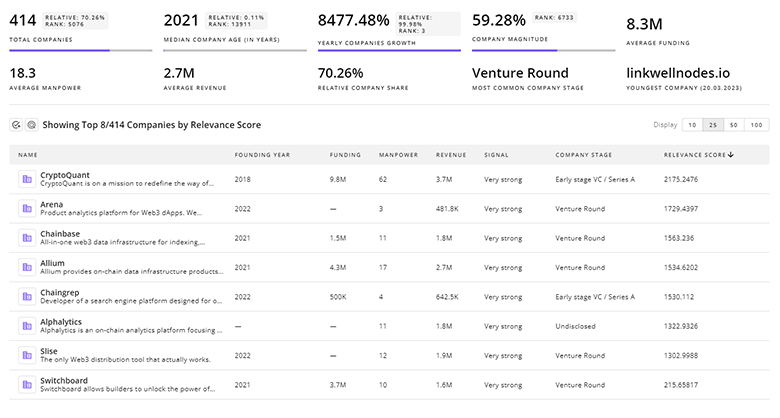
2.6K Business Security Companies
Discover Business Security Companies, their Funding, Manpower, Revenues, Stages, and much more
Business Security Investors
TrendFeedr’s investors tool offers a detailed view of investment activities that align with specific trends and technologies. This tool features comprehensive data on 133 Business Security investors, funding rounds, and investment trends, providing an overview of market dynamics.
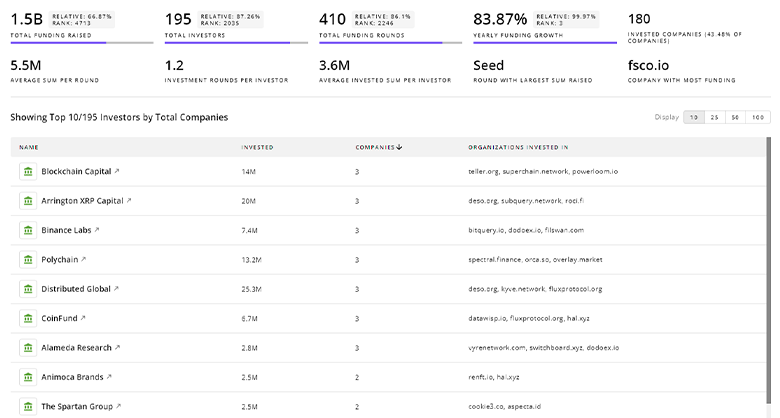
133 Business Security Investors
Discover Business Security Investors, Funding Rounds, Invested Amounts, and Funding Growth
Business Security News
Stay informed and ahead of the curve with TrendFeedr’s News feature, which provides access to 4.6K Business Security articles. The tool is tailored for professionals seeking to understand the historical trajectory and current momentum of changing market trends.
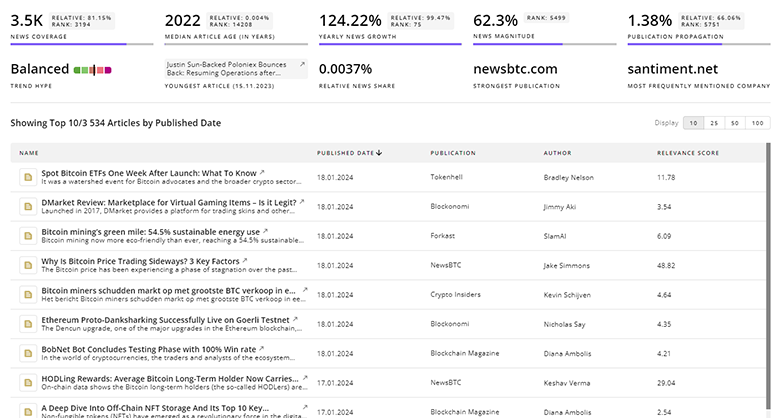
4.6K Business Security News Articles
Discover Latest Business Security Articles, News Magnitude, Publication Propagation, Yearly Growth, and Strongest Publications
Executive Summary
The business security sector is a robust and evolving landscape where innovation meets necessity. Companies are actively adopting cutting-edge technologies such as AI, cloud computing, and IoT to provide sophisticated security solutions. The rise in cyber threats has catalyzed the growth of cybersecurity measures, while physical security remains a steadfast concern. The integration of various security disciplines into cohesive systems offers businesses a comprehensive approach to risk mitigation. As the sector continues to expand, driven by investments and technological advancements, businesses are well-positioned to enhance their security posture and protect their most valuable assets against an array of threats.
Interested in enhancing our coverage of trends and tech? We value insights from experts like you - reach out!